Date: 2024-12-13 16:53 | Source: TheAIGRID

Summary:
Google's Gemini Advanced 1.5 Pro deep research tool automates comprehensive online research, providing step-by-step plans and compiling data into detailed reports, significantly enhancing efficiency for internet users.
Main Points:
- Gemini Advanced 1.5 Pro offers automated, detailed research capabilities for internet users.
- Users can customize research plans and include specific data sources like Reddit.
- The tool efficiently compiles data from multiple online sources into comprehensive reports.
- It eliminates the need for manual browsing, saving users significant time and effort.
Key Takeaways:
- Activate the tool by selecting the 1.5 Pro model with deep research from the menu.
- Customize research plans to include specific sources or steps as needed.
- The tool uses multiple agents to gather data from various online platforms.
- Users receive a comprehensive report without needing to manually browse numerous websites.
Date: 2024-12-13 16:51 | Source: techcrunch.com
Summary:
Liquid AI, co-founded by Daniela Rus, raised $250 million in a Series A led by AMD, valuing it over $2 billion, to develop general-purpose AI systems using liquid neural networks.
Main Points:
- Liquid AI, co-founded by Daniela Rus, focuses on developing general-purpose AI systems.
- The startup raised $250 million in a Series A funding round led by AMD.
- Liquid AI is valued at over $2 billion following the latest funding round.
- The company utilizes liquid neural networks, a relatively new AI model type.
Key Takeaways:
- Liquid AI's significant funding highlights investor confidence in their innovative AI approach.
- The involvement of AMD as a lead investor suggests strategic interest in AI advancements.
- Liquid neural networks represent a promising new direction in AI model development.
- The high valuation underscores the potential impact of Liquid AI's technology in the AI industry.
Date: 2024-12-13 16:25 | Source: packetpushers.net
Summary:
Heavy Networking from AutoCon2 features a roundtable discussion with four network automators on crafting tools for network automation.
Main Points:
- The episode was recorded at AutoCon2 in Westminster, Colorado, in November 2024.
- A roundtable format was used for the discussion.
- Four network automators participated, each bringing their own topics.
- The focus was on creating tools to improve network automation.
Key Takeaways:
- AutoCon2 serves as a platform for network automation discussions.
- The roundtable format encourages diverse viewpoints and collaborative problem-solving.
- Participants are actively involved in shaping the future of network automation.
- Crafting effective automation tools is a key focus for network professionals.
Date: 2024-12-13 15:04 | Source: Fireship

Summary:
Devon, an AI tool for automating coding tasks, offers potential cost savings and efficiency but faces skepticism due to unclear capabilities and typical AI quirks.
Main Points:
- Devon is an AI tool marketed as a cost-effective alternative to junior engineers, priced at $500 per month.
- Despite its promise, Devon's actual capabilities remain vague, with no clear benchmarks or scientific validation.
- The tool operates through Slack, targeting non-programmers in enterprise settings to automate coding tasks.
- Devon can write, test, and deploy code, but exhibits typical AI issues like unnecessary code changes and hallucinations.
Key Takeaways:
- Devon aims to replace junior engineers by automating coding tasks more efficiently and affordably.
- The tool's integration with Slack is designed for enterprise users, not traditional developers.
- Despite its potential, Devon's performance and reliability remain questionable due to lack of transparency.
- Users should be cautious of AI quirks, such as hallucinations and unnecessary changes, when using Devon.
Date: 2024-12-13 14:12 | Source: arstechnica.com
Summary:
AI-generated videos often exhibit nonsensical movements due to limitations in current technology and algorithms, as demonstrated by OpenAI's Sora.
Main Points:
- AI-generated video technology is still developing, leading to unrealistic and nonsensical movements.
- OpenAI's Sora exemplifies the typical challenges faced in creating coherent AI video content.
- Current algorithms struggle with understanding complex motion and context in video generation.
- Improvements in AI video generation require advancements in both technology and algorithmic understanding.
Key Takeaways:
- AI video generation is an emerging field with significant room for improvement.
- Understanding and replicating realistic motion in AI videos remains a major challenge.
- OpenAI's Sora highlights the current state and limitations of AI video technology.
- Future advancements could lead to more coherent and realistic AI-generated video content.
Date: 2024-12-13 11:23 | Source: dcnnmagazine.com
Summary:
STULZ has announced the CyberAir Mini DX, a space-saving air conditioning solution for small to medium heat loads, launching in January 2025.
Main Points:
- STULZ introduces the CyberAir Mini DX for small and medium heat loads.
- Launch date for the CyberAir Mini DX is set for January 2025.
- The new range complements the existing CyberAir Mini CW series.
- CyberAir Mini DX and CW will replace the MiniSpace series.
Key Takeaways:
- STULZ is focusing on space-saving air conditioning solutions.
- The CyberAir Mini DX targets small to medium-sized heat loads.
- The launch marks a strategic update to STULZ's product lineup.
- Transition from MiniSpace to CyberAir Mini series indicates innovation.
Date: 2024-12-13 11:00 | Source: IBM Technology

Summary:
The Mixture of Experts podcast discusses the new $200/month o1 Pro AI model from OpenAI, with differing opinions on its value and potential adoption among AI professionals.
Main Points:
- OpenAI has introduced a $200/month tier for their o1 Pro AI model, aiming to increase adoption.
- Vyoma Gajjar supports the subscription, citing benefits like reduced latency and higher speed for developers.
- Kate Soule opposes the cost, arguing it doesn't align with typical usage patterns for AI models.
- The discussion highlights differing perspectives on whether the o1 Pro is a luxury product or a necessary tool.
Key Takeaways:
- OpenAI's strategy aims to reach 1 billion users by 2025, promoting wider AI adoption.
- The o1 Pro model is marketed as a premium product with enhanced features for developers.
- Some professionals see the high cost as unjustifiable for everyday AI tasks.
- The debate reflects broader questions about the value and accessibility of advanced AI technologies.
Date: 2024-12-13 10:11 | Source: techcrunch.com
Summary:
WhatsApp introduces enhanced video calling features, such as participant selection and improved resolution, to compete with platforms like Google Meet for personal and work calls.
Main Points:
- WhatsApp has added new video calling features before the holidays.
- Features include participant selection for group video calls.
- Improved resolution is part of the new updates.
- A revamped call tab is now available on the desktop.
Key Takeaways:
- WhatsApp aims to be a competitive option for both personal and work calls.
- The updates are part of Meta's strategy to enhance WhatsApp's functionality.
- These features position WhatsApp as an alternative to Google Meet.
- The enhancements are designed to improve user experience on both mobile and desktop.
Date: 2024-12-13 09:00 | Source: techcrunch.com
Summary:
Syndicate One, a debut Belgian investment firm, has raised a €6.5 million fund to support Belgian startups, uniquely backed by all four federal regions.
Main Points:
- Syndicate One is a new investment firm based in Belgium.
- The firm has raised a €6.5 million fund for Belgian startups.
- It is the first Belgian fund supported by all four federal regions.
- The fund aims to back Belgian founders and startups.
Key Takeaways:
- Syndicate One's fund represents a collaborative effort across Belgium's federal regions.
- The €6.5 million fund, though modest, marks a significant regional investment milestone.
- This initiative could inspire similar regional collaborations in other countries.
- Belgian startups now have a new source of financial support through Syndicate One.
Date: 2024-12-13 08:00 | Source: TheAIGRID

Summary:
Google, in collaboration with Samsung and Qualcomm, launched Android XR, a platform enhancing reality through headsets and glasses, integrating AI for daily use and offering advanced tools for developers.
Main Points:
- Android XR extends reality beyond traditional screens, leveraging AI for daily applications.
- The platform supports headsets and glasses, offering tools for developers and reducing usage friction.
- Collaboration with Samsung and Qualcomm enhances software, UX, and hardware integration.
- Key technologies include AR core, geospatial API, and Gemini, enhancing user experiences.
Key Takeaways:
- Android XR represents a significant shift in computing, moving beyond screens to immersive experiences.
- The collaboration between Google, Samsung, and Qualcomm is crucial for the platform's success.
- Glasses are designed for all-day use, providing continuous value and connectivity.
- The platform's development involves deep collaboration with developers, designers, and device makers.
Date: 2024-12-13 08:14 | Source: blog.ipspace.net
Summary:
Sometimes using suboptimal BGP practices, like disaggregated prefixes, is necessary when dealing with ISPs unfamiliar with BGP communities.
Main Points:
- Optimal BGP usage may be compromised due to ISP limitations.
- Disaggregated prefixes can be a necessary solution.
- A BGP lab exercise is available to practice this approach.
- Lab setup can be done via GitHub Codespaces or personal infrastructure.
Key Takeaways:
- BGP communities may not always be understood by ISPs.
- Disaggregated prefixes act as a workaround for BGP issues.
- Practical exercises enhance understanding of BGP configurations.
- Flexible lab setup options support diverse user preferences.
Date: 2024-12-13 06:33 | Source: blog.apnic.net
Summary:
The APNIC Executive Council has released its official response to the findings and recommendations from the 2024 APNIC Survey.
Main Points:
- The response addresses key concerns and suggestions raised by the APNIC community.
- It outlines strategic actions to improve APNIC services and operations.
- The document emphasizes transparency and accountability in addressing survey feedback.
- It highlights ongoing and future initiatives to enhance member engagement and satisfaction.
Key Takeaways:
- APNIC is committed to acting on community feedback to improve its services.
- The Executive Council prioritizes transparency in its decision-making processes.
- Strategic initiatives are in place to boost member engagement.
- Future plans focus on enhancing operational efficiency and member satisfaction.
Date: 2024-12-13 01:00 | Source: techcrunch.com
Summary:
Microsoft introduces Phi-4, an advanced generative AI model with enhanced math problem-solving capabilities, attributed to improved training data quality, available in limited access.
Main Points:
- Microsoft launched Phi-4, the latest in its generative AI model series.
- Phi-4 shows significant improvements, especially in solving math problems.
- Enhanced training data quality contributes to Phi-4's advancements.
- Limited access to Phi-4 began on Thursday night.
Key Takeaways:
- Phi-4 represents a major step forward in Microsoft's AI capabilities.
- The model's enhanced math skills highlight its potential for educational applications.
- Improved data quality is crucial for advancing AI model performance.
- Limited release suggests a cautious rollout strategy by Microsoft.
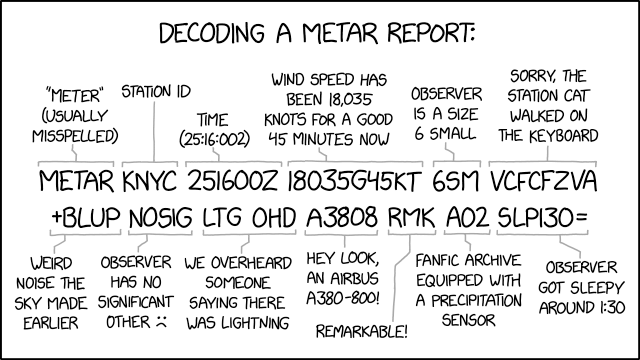
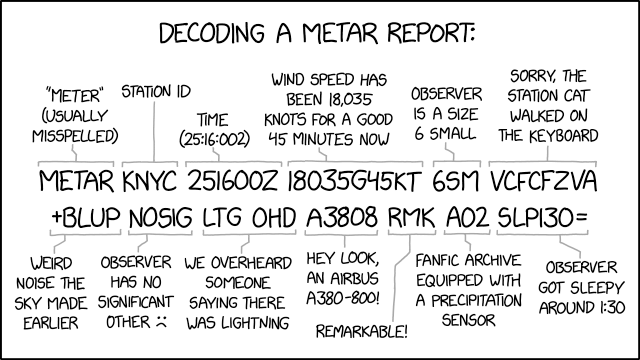
Date: 2024-12-13 00:00 | Source: xkcd.com
Date: 2024-12-13 00:00 | Source: techcrunch.com
Summary:
Meta has introduced Meta Video Seal, an open-source method for watermarking AI-generated videos, designed to withstand compression and edits.
Main Points:
- Meta Video Seal is a new method for watermarking AI-generated videos.
- The watermarking technique is being open-sourced by Meta.
- It is designed to be robust against video compression.
- The method can withstand various video edits.
Key Takeaways:
- Meta is contributing to the transparency of AI-generated content.
- Open-sourcing the watermarking method encourages widespread adoption.
- The robustness against compression ensures video integrity.
- Resistance to edits enhances the reliability of the watermark.
Date: 2024-12-12 21:15 | Source: arstechnica.com
Summary:
Character.AI's latest model aimed at teenagers addresses some issues but fails to alleviate all parental concerns regarding safety and content appropriateness.
Main Points:
- Character.AI released a new model specifically designed for teenage users.
- The model aims to address safety and content concerns for younger audiences.
- Despite improvements, the model does not fully satisfy all parental worries.
- Parents remain cautious about the model's effectiveness in protecting teens.
Key Takeaways:
- The new model represents Character.AI's effort to cater to a younger demographic.
- Safety and content appropriateness are central to the model's design.
- Parental concerns highlight the ongoing challenge of ensuring online safety for teens.
- Continued development is necessary to fully address parental apprehensions.
Date: 2024-12-12 21:00 | Source: arstechnica.com
Summary:
A critical vulnerability with a severity rating of 9.8 out of 10 remains active on over 8,000 websites.
Main Points:
- A vulnerability with a high severity rating of 9.8 is still present.
- Over 8,000 websites are affected by this security issue.
- The vulnerability poses significant risks due to its critical nature.
- Immediate action is required to address and mitigate the threat.
Key Takeaways:
- Website administrators must prioritize addressing this critical vulnerability.
- Regular security audits can help identify and fix such vulnerabilities.
- Awareness of website security status is crucial for preventing breaches.
- Proactive measures are essential to protect against high-severity vulnerabilities.
Date: 2024-12-12 20:45 | Source: techcrunch.com
Summary:
Yahoo has reduced its cybersecurity team, The Paranoids, by approximately 25% over the past year.
Main Points:
- Yahoo's cybersecurity team is called The Paranoids.
- The company laid off about 25% of this team.
- These layoffs occurred over the last year.
- The information is reported by TechCrunch.
Key Takeaways:
- Yahoo is restructuring its cybersecurity workforce.
- The Paranoids team faced significant staff reductions.
- Layoffs indicate possible strategic shifts in Yahoo's cybersecurity approach.
- TechCrunch provided the report on these developments.
Date: 2024-12-12 20:08 | Source: WorldofAI

Summary:
The demo showcases an AI-powered travel application built using Lang graph and Copilot Kit, highlighting agented copilot capabilities for effective human-AI collaboration in real-world applications.
Main Points:
- The demo illustrates an AI travel application using Lang graph and Copilot Kit.
- Agented copilot combines AI assistants, autonomous programs, and human workflows.
- Features include agentic UI, shared state, and state streaming.
- Copilot Kit supports AI integration with tools like Lang chain and co-agents.
Key Takeaways:
- Agented copilots offer more effective solutions than fully autonomous AI agents.
- Lang graph and Copilot Kit enable quick development of agent-native applications.
- Human-in-the-loop workflows enhance productivity and decision-making.
- Copilot Kit provides customizable AI capabilities with real-time data integration.